BREAKING: Amazon Senior Security Engineer Indicted in $9M Crypto Heist
This guy wasn't smart. Not at all

This guy wasn't smart. Not at all
In a dramatic twist, Shakeeb Ahmed, 34, of Louisville, KY, was arrested in Manhattan and indicted today by the Department of Justice in the Southern District of New York for orchestrating a cryptocurrency heist worth millions which occurred last year.
Ahmed stands accused of illegally manipulating systems in yet another case involving alleged misuse of technical expertise by the type of person typically entrusted to protect them. The indictment paints a picture of a man who, instead of using his technical acumen as a Senior Security Engineer at Amazon to promote the security of digital assets, decided to exploit them for personal gain, and was determined to get away with it.
The case was described by US Attorney Damian Williams (Same lawyer behind the successful prosecution of Ghislaine Maxwell), on Twitter as "the first-ever criminal case involving an attack on a smart contract operated by a decentralized cryptocurrency exchange".
0:00
Notably, this attack took place on the Solana blockchain, which has not been synonymous with security breaches, yet is seeing growing interest from hackers due to its rising position within the cryptocurrency industry.
IRS-CI Special Agent in Charge Tyler Hatcher said:
“As alleged, Mr. Ahmed used his skills as a computer security engineer to steal millions of dollars. He then allegedly tried to hide the stolen funds, but his skills were no match for IRS Criminal Investigation's Cyber Crimes Unit. We, along with our partners at HSI and the Department of Justice, are at the forefront of cyber investigations and will track these fraudsters anywhere they try to hide and hold them accountable.”
I found the inclusion and prominence of the IRS Criminal Investigation (IRS-CI) division in the indictment to be interesting, as they were recently in the news for working with crypto investigations company Chainalysis (an investigative firm of growing global importance) and the Ukrainian Government to "target Russian oligarchs who may be using crypto to evade sanctions".
My hunch is IRS-CI used one or more Chainalysis product(s) such as Reactor to perform blockchain analysis to help solve this case.
The charges against Ahmed are:
Wire Fraud: Ahmed is accused of devising a scheme to defraud Crema Finance and its users by obtaining cryptocurrency through false and fraudulent means. The indictment alleges that Ahmed transmitted and caused to be transmitted fraudulent information.
Money Laundering: Ahmed is charged with knowingly conducting financial transactions involving the proceeds of unlawful activity. The indictment asserts that Ahmed engaged in transactions that aimed to conceal and disguise the nature, source, ownership, and control of the fraudulently obtained funds.
According to the indictment, Ahmed, a U.S. citizen residing in Manhattan, New York, orchestrated the scheme in July 2022.
According to his LinkedIn profile, Ahmed has held three security-focused roles since 2015 as a Security Researcher, Principal Security Researcher, and Senior Security Engineer at NYC security startup Red Balloon Security, private security firm Optiv, and Amazon, respectively.
The latter is listed as his current employer.

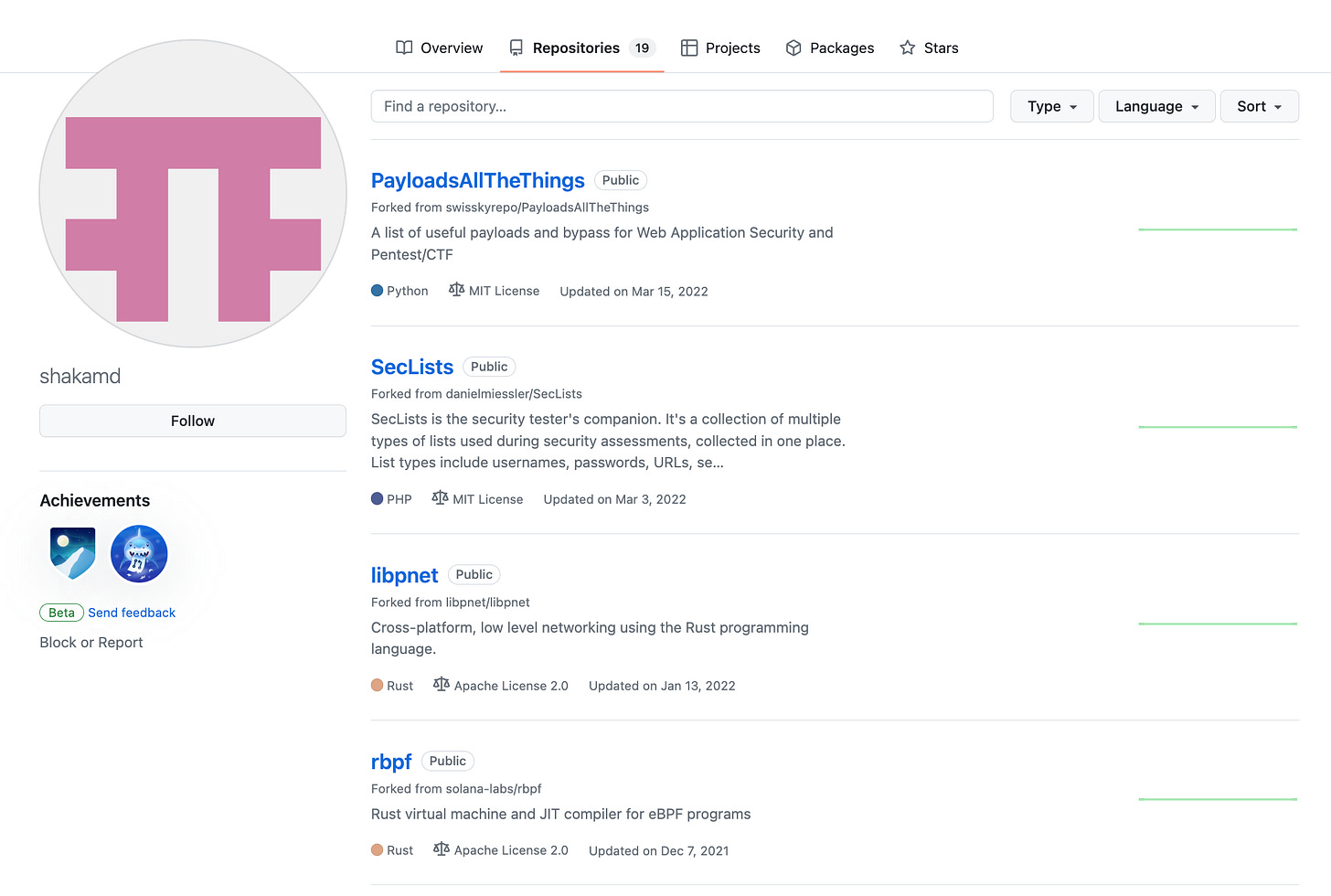
While Ahmed does not have much of a professional presence, and his Github account is sparse with no public code of his own, I was able to identify two forks of Solana-related code on his Github.
What is he accused of doing?
Ahmed allegedly exploited a vulnerability in a decentralized cryptocurrency exchange's system, inserting fake pricing data to generate millions of dollars' worth of inflated fees that he did not earn. The indictment alleges that Ahmed used his skills in reverse engineering smart contracts and conducting blockchain audits to execute the attack.
Ahmed allegedly created two fake accounts that masqueraded as "tick accounts"; accounts owned and controlled by the exchange that contained data about the liquidity provided by all liquidity providers for a particular price range. He used these accounts to fraudulently cause the exchange's smart contract to accept them as legitimate tick accounts, thereby generating large fees for himself that he had not legitimately earned.
The indictment further alleges that Ahmed took out a series of uncollateralized cryptocurrency "flash loans" worth tens of millions of dollars from a crypto lending platform. He deposited the funds from these loans into the exchange's liquidity pools, withdrew the funds, claimed a falsely inflated percentage of the loans as fees from the exchange through his deceptive use of the fake tick accounts, and then repaid the loans to the lender.
Following the attack, Ahmed allegedly laundered the stolen crypto through a series of transactions designed to conceal the source and owner of the funds. These included conducting token-swap transactions, "bridging" fraud proceeds from the Solana blockchain over to the Ethereum blockchain, exchanging fraud proceeds into Monero (an anonymized and particularly difficult cryptocurrency to trace), and using overseas crypto exchanges.
The indictment also details Ahmed's alleged attempts to negotiate with the exchange following the attack.
The exchange, realizing it had been exploited, attempted to negotiate with the still-unidentified hacker.
The exchange offered a sum of $800,000 for the return of all stolen funds, a move that underscored the severity of the situation. However, Ahmed, demonstrating a brazen disregard for the potential legal consequences, decided to keep a significantly larger portion of the stolen cryptocurrency. He offered to provide information about the exchange's technical vulnerabilities and proposed to retain approximately $2.5 million of the stolen funds, later reducing his demand to $1.8 million, and finally settling on keeping around $1.5 million.
These moves seem to highlight the unplanned nature of Ahmed's crimes and his inexperience with handling large sums of illicit funds, but also reveals some of the challenges faced by technology companies dealing with security breaches and their aftermath.
Despite Shakeeb Ahmed's technical prowess, which allowed him to exploit a complex decentralized cryptocurrency exchange and steal millions, his actions post-attack revealed a glaring lack of foresight and understanding of the digital footprint he was leaving behind. His technical acumen clearly did not extend to the realm of digital privacy and law enforcement capabilities.
💡
His internet search history, which included terms like "defi hack," "embezzled," "wire fraud," and "how to prove malicious intent," as well as searches about fleeing the United States and avoiding asset seizure, seem to paint a picture of guilt and panic.
These actions, far from the calculated precision of his initial attack, demonstrated a surprising naïveté about the traceability of Internet and blockchain activities.
Timeline
July 2022: Shakeeb Ahmed conducts a series of test transactions with the Crypto Exchange to obtain tick data and locate system vulnerabilities.
July 2, 2022: Ahmed creates the First Fake Tick Account and enters fake price-tick data into it. He then takes out a series of cryptocurrency flash loans from a cryptocurrency lending platform and uses them to generate falsely inflated fees from five separate liquidity pools controlled by the Crypto Exchange.
🚨🚨Attention! Our protocol seems to have just experienced a hacking. We temporarily suspended the program and are investigating it. Updates will be shared here ASAP.
— CremaFinance (@Crema_Finance) July 3, 2022
July 3, 2022: Ahmed allegedly creates the Second Fake Tick Account to withdraw the principal he owed and return it to the Crypto Lender. The Crypto Exchange, Crema Finance, initiates public communications on the blockchain with Ahmed (unidentified at the time) to seek the return of the stolen funds. Organizations begin to add the attacker's wallets to community blocklists after the initial Solana wallet was tracked down.

July 5, 2022: Ahmed allegedly visits or searches for information about the attack on the internet. He also visits a news article describing a $10 million bounty that a cryptocurrency bridging platform had paid. Before communicating with the Crypto Exchange, Ahmed visits or searches for information about white-collar criminal defense attorneys with expertise in cryptocurrency.
July 6, 2022: Ahmed allegedly contacts the Crypto Exchange and states that he would return a portion of the stolen funds if the Crypto Exchange agreed not to refer the attack to law enforcement.
July 7, 2022: Ahmed indicates that he intends to keep $1.8 million of the stolen cryptocurrency and states that he would provide details on two purported vulnerabilities in the Crypto Exchange's platform. Later that same day, Ahmed returns all but approximately $1.5 million of the fraudulently obtained cryptocurrency to the Crypto Exchange.
July 8, 2022: Ahmed purportedly provides information to the Crypto Exchange about their technical vulnerabilities.
July–December 2022: Ahmed visits or searches for information about whether he is likely to be prosecuted for the attack. He also visits or searches for information about his ability to flee the United States, avoid extradition, and keep his stolen cryptocurrency.
November 5, 2022: Ahmed exchanges fraud proceeds into the cryptocurrency Monero.
May 2023: Ahmed launders fraud proceeds through overseas cryptocurrency exchanges.
Technical Details
The attack was a sophisticated exploitation of the vulnerabilities inherent in the Crema Finance's Concentrated Liquidity Market Maker (CLMM).
1) It's been a tough day. Here we would like to give a recap of the recent hacking we just suffered from and share the information that we have in hands with all our users and Solana audience with transparency.
— CremaFinance (@Crema_Finance) July 3, 2022
The attack began with Ahmed creating a fake tick account. In the context of CLMM, a tick account is a dedicated account that stores price tick data, which is crucial for calculating transaction fees. Ahmed was able to bypass the routine owner check on the tick account by writing the initialized tick address of the pool into the fake account.
This essentially tricked the system into accepting the fake tick account as legitimate.
Once the fake tick account was established, Ahmed deployed a contract and used it to secure a flash loan from Solend, a cryptocurrency lending platform. He then used the funds from this flash loan to add liquidity to Crema Finance and open positions. The positions were opened in such a way that they would trigger the fake price tick data in the fake tick account.
The crux of the attack lay in the manipulation of transaction fee data.
In Crema Finance's CLMM, the calculation of transaction fees is heavily dependent on the data in the tick account. By replacing the authentic transaction fee data with the faked data in the fake tick account, Ahmed was able to claim an inflated fee amount from the pool. This essentially allowed him to steal a significant amount of cryptocurrency from the exchange.
In response to the attack, Crema Finance suspended its smart contract (a feat made possible due to Solana's inherent technical characteristics, chiefly program upgradeability) and began working with third parties to track the movements of the hacker's funds. Ahmed was able to launder the stolen funds, converting them into 69,422.9 SOL and 6,497,738 USDCet via Jupiter. The USDCet was then bridged to the Ethereum network via Wormhole and swapped for 6064 ETH via Uniswap.
This complex series of transactions further obfuscated the trail of the stolen funds, leading authorities to use advanced blockchain analytics software, presumably Chainalysis Reactor as described earlier in this piece, to reach an indictment.
Conclusion
The case highlights the risks associated with the decentralized nature of cryptocurrency exchanges, which do not rely on any entity or company to act as an intermediary between buyers and sellers. Instead, they use "smart contracts" associated with "liquidity pools" to serve as an "automated market maker." While this structure can offer benefits such as increased privacy and reduced costs, it also opens the door to potential vulnerabilities, as demonstrated by Ahmed's alleged scheme.
As the case proceeds, it will undoubtedly serve as a critical test of the ability of law enforcement and the courts to adapt to the complexities of cryptocurrency fraud and bring those who exploit these systems to justice.
This case also highlights the potential for misuse when technical expertise is coupled with criminal intent, highlighting the need for robust security measures and stringent oversight in the rapidly evolving cryptocurrency industry.
Update: Ahmed has pled "not guilty".
Judge: He will reside in [address on 57th Street]
Case is assigned to District Judge Victor Marrero.
Ahmed's T-shirt says "I Code"
Story coming.— Inner City Press (@innercitypress) July 11, 2023
Thanks for reading!
Don't miss updates, subscribe for free! 👈
