EXCLUSIVE: The Architecture of Erasure
How Trump's executive orders on DEI are dismantling American cybersecurity — one accountability structure at a time
In July 2025, the acting director of the nation’s civilian cyberdefense agency walked into a secure facility for a counterintelligence polygraph and did not pass.
Five current officials and one former official later confirmed this to Politico. Then, he took it again. He did not pass the second time either. Within days of the first result, the employees who had arranged the examination and done nothing more than follow the security requirements of the originating intelligence agency received letters suspending their access to classified information. The acting director kept his badge, but the staffers who enforced the rules lost theirs.

That sequence of events, which received scattered coverage when it broke into public view last December, is the right place to start a story about an executive order that President Trump signed on March 26, 2026 — and about what has happened to the federal networks those staffers were paid to protect.
On April 1, 2026, the FBI notified Congress that Chinese hackers had breached one of its internal surveillance systems in what the bureau classified as a “major incident” under FISMA. The compromised system, known internally as DCS-3000, is a pen register and trap-and-trace collection network that stores metadata revealing who the FBI is watching: which phone numbers, which websites, which subjects of active counterintelligence investigations. The intrusion was traced to a third-party commercial internet service provider’s vendor infrastructure. It was, in other words, a supply-chain attack — the exact category of threat that Emergency Directive 21-01 was written to address, and that CISA retired in a bulk action on January 8, 2026, three weeks after the polygraph story broke. The CISA story, the DEI story, and the FBI breach story are the same story.
Understanding why requires going back to the beginning.
Sixty Years of Scaffolding
Lyndon Johnson signed Executive Order 11246 on September 24, 1965, in the middle of a decade that had already produced the Civil Rights Act and the Voting Rights Act. His order required federal contractors to do more than refrain from discrimination: they had to take affirmative steps to remedy it. Any company with a federal contract above $50,000 and at least 50 employees was obligated to develop a written Affirmative Action Program — an annual document specifying hiring goals, promotion timelines, pay equity analyses, and self-audits. A Labor Department bureau called the Office of Federal Contract Compliance Programs existed to enforce this, and in 2024 it was still recovering millions from contractors for alleged violations.
President Johnson’s theory was structural, rather than sentimental.
A labor market shaped by decades of exclusion from schools, professional networks, and institutions would, if left to its own devices, reproduce that exclusion through criteria that looked neutral but weren’t. The correction factor had to be built in. For sixty years, through administrations of both parties, through the Reagan era’s attempts to weaken it, the Clinton era’s “mend it, don’t end it” compromise, and Bush and Obama tenures where it remained effectively untouched, EO 11246 held.
On January 21, 2025, it was revoked.
The First Demolition
Trump’s second inaugural week produced two executive orders relevant here.
The first, EO 14151 (“Ending Radical and Wasteful Government DEI Programs”), was largely an internal matter: federal agencies were told to shutter their DEI offices, eliminate equity grants and contracts, and remove diversity requirements from employee performance reviews. Federal DEI staff were placed on administrative leave within days. The second order on the following day, EO 14173 (“Ending Illegal Discrimination and Restoring Merit-Based Opportunity”), did the structural work.
It abolished Johnson’s EO 11246 outright, dismantled OFCCP’s enforcement authority, and replaced sixty years of affirmative action mandate with a certification requirement: every new federal contract would have to include a contractor’s attestation that it was not running DEI programs in violation of anti-discrimination law. The certification clause carried a second provision that drew less attention at the time.
It stated that compliance was “material to the Government’s payment decisions” under the False Claims Act — the Civil War-era statute that authorizes the government to recover treble damages from contractors who defraud it. The FCA also allows private citizens to file suit on the government’s behalf and keep a share of what’s recovered. Those suits, called qui tam actions, are the mechanism through which the administration intends to make an example of holdouts. The White House’s FY2026 budget proposal sought to eliminate OFCCP, removing its EO 11246 enforcement authority, but Congress ultimately funded the agency at roughly $101 million in the Consolidated Appropriations Act of 2026, leaving it smaller, narrowed, and focused on a much thinner slice of contractor compliance.
Courts moved immediately. A Maryland district judge issued a nationwide preliminary injunction in February 2025, concluding that key provisions were likely unconstitutional, and the administration appealed. The Fourth Circuit stayed the injunction, then vacated a second one. On February 6, 2026, the court ruled in NADOHE v. Trump that the orders could not be struck down wholesale. Challengers would have to contest specific enforcement actions as they arose.
The orders have been fully operative ever since.
The Enforcement Machinery
In May 2025, Deputy Attorney General Todd Blanche announced what DOJ called the Civil Rights Fraud Initiative, pairing the Civil Fraud Section and the Civil Rights Division to pursue FCA actions against contractors whose DEI programs could be characterized as race-conscious. The legal theory was not complicated: a company that submits a payment request to the government certifies, implicitly, that it is complying with applicable law. If prohibited programs are maintained while collecting federal payments, every invoice is a false claim. By December 2025, DOJ had issued civil investigative demands (subpoenas for documents and testimony) to companies across finance, defense, technology, and healthcare.
The FCA set a record in FY2025 by “recovering” $6.8 billion. This was the largest annual total in the statute’s 160-year history, more than doubling the prior year’s $2.9 billion. DOJ’s press release announcing the figure specifically cited EO 14173 as an enforcement priority for FY2026.
One thousand two hundred ninety-seven (1,297!) qui tam suits were filed in FY2025 alone.
The Newest Order
The executive order signed a little more than a week ago is the campaign’s third instrument, and it addresses something the administration has evidently concluded the prior framework failed to prevent.
The White House fact sheet states this candidly: “some entities, including government contractors, have attempted to conceal ongoing DEI activities even as the Administration has worked to end them.”
Where EO 14173 asked contractors to certify their own compliance, the order requires that every covered contract contain a verbatim clause prohibiting “racially discriminatory DEI activities”, defined as disparate treatment in hiring, promotion, contracting, or program participation based on race or ethnicity as a condition of performance. FCA materiality language, previously embedded in guidance, is now written into the contract clause itself. Contractors must also report any subcontractor’s known or “reasonably knowable” violations up the chain of command. This is a reporting duty that runs opposite to the usual flow of federal oversight, from contractor employee to contracting agency, and bypasses the subcontractor’s own management.
The order covers only race and ethnicity, conspicuously omitting sex, sexual preference, religion, and national origin that appeared in EO 14173.
Gender-based DEI programs such as women’s leadership tracks and pay equity reviews are left to the broader regulatory environment. The Office of Management and Budget is directed to identify specific sectors at particular risk of violations based on past conduct and issue sector-specific guidance. Finance, defense, technology, and healthcare have already been named in prior DOJ statements.
Cybersecurity contractors, defense-adjacent and technology-forward, are obvious candidates for early targeting.
What Has Already Changed
Since Trump’s re-election in November 2024, roughly one in five U.S. companies has eliminated DEI programs.
Among those, fifty-seven percent reported hiring fewer workers from underrepresented groups, and a third reported promoting fewer. Representation of people of color in leadership fell at thirty percent of the companies that cut programs; women’s leadership representation fell at twenty-four percent. The Conference Board found that fifty-three percent of S&P 100 companies changed how they described DEI efforts in their 2025 regulatory filings. Mentions of the acronym “DEI” in Fortune 100 documents fell ninety-eight percent year over year; broader references to diversity dropped seventy-two percent. Much of what corporate America has done is not eliminate programs but rename them. This looks more like a retreat from transparency in an attempt to appear compliant with Trump’s rulings rather than a genuine retreat from actual practice.
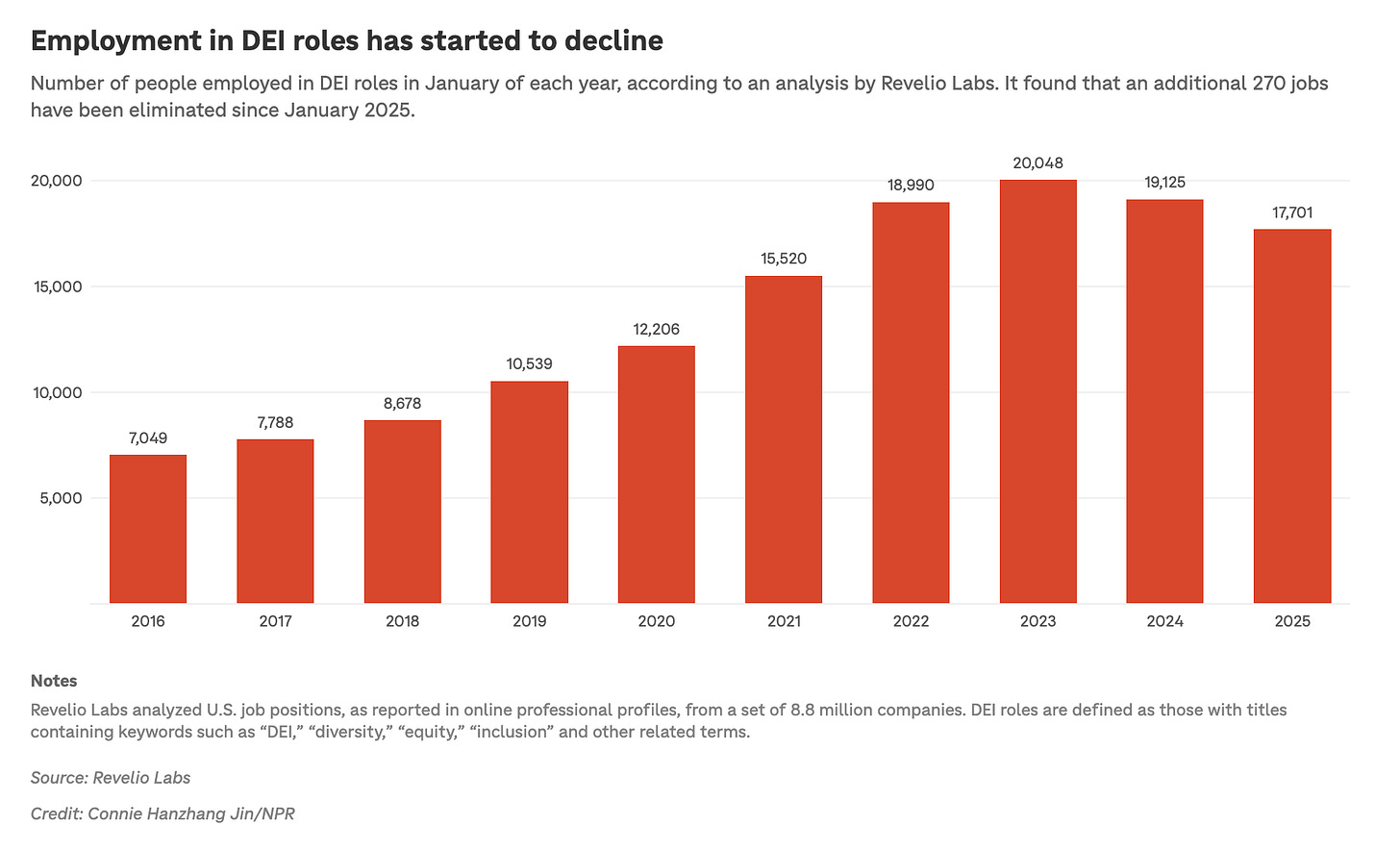
More than twenty-six hundred jobs carrying “diversity” or “DEI” in the title have been eliminated since early 2023. The Pentagon cut or restructured a hundred and eighty-eight related positions.
The financial consequences have been real, yet unevenly distributed.
Target announced its DEI rollbacks in January 2025 and experienced more than two hundred days of declining performance: ten consecutive weeks of declining foot traffic, a missed first quarter, and an estimated twenty billion dollars in market capitalization erased by the time the full impact registered. Investors sued, alleging the company had misled shareholders about the financial risks of the decision itself, which was the first time a rollback decision generated securities litigation, inverting the conventional risk calculation entirely. Costco, which defended its commitments publicly during the same period of shareholder pressure, saw between 4.6% and 5.8% year-over-year foot traffic growth.
The CISA Catastrophe
CISA entered fiscal year 2025 with approximately 3,732 employees. The FY2026 budget proposal sought to reduce CISA’s staffing to 2,324 positions. What actually happened through layoffs, buyouts, and people who left without prompting because the environment had become untenable, brought headcount even lower to around 2,200 by mid-2025 — a loss of roughly a third.
About seventy staff were reassigned to other DHS components, including ICE, through management-directed transfers. The Cybersecurity Division, which monitors federal networks for intrusions, fell from around 1,100 people to around 800-850. CISA’s nationwide team of Cybersecurity Advisers — the field staff who connect companies with federal resources — went from 164 to about 97. The Stakeholder Engagement Division faced a sixty-two percent funding reduction; the National Risk Management Center, which provided cross-sector risk analysis, faced seventy-three percent.
In April, CISA announced it is planning to hire more than three hundred people. A familiar mechanism runs through both the CISA story and the DEI orders: remove the structure that enforced rules, wait to see what falls away, then propose to rebuild from a narrower base, under worse conditions, without restoring the safeguards that kept the enterprise functioning in the first place.
How Gottumukkala Got There
Madhu Gottumukkala arrived as acting director in May 2025, installed by Secretary Kristi Noem. His career had moved from Motorola and Verizon consulting to Samsung engineering to a CTO post at CallHealth in Hyderabad, then to Sanford Health, then to South Dakota state government as CIO. None of those roles required navigating the culture or methods of the intelligence community. Dakota State University — where Gottumukkala completed his PhD and later joined the advisory board — holds all three NSA Center of Academic Excellence designations and hosts an on-campus SCIF. To whoever placed him, that combination may have read as a credential. The substantive career remained in civilian IT and healthcare.
Within weeks of his arrival, Politico reported that in his first major intelligence briefing, he asked what threats the U.S. faced from the Southern border and India — a country that has never been considered a significant cyber adversary, while Russia and China were actively targeting American networks.
“Typically, India would be the last place we’d be talking about,” said one official who was in the room.
He also, within weeks of arrival, began pressing for access to a Controlled Access Program — among the most restricted intelligence compartments in existence, established only when ordinary Special Access Programs are insufficient, governed by the Director of National Intelligence, with entry conditions set by the originating agency. A senior career official denied the first request: there was no operational need, and his predecessor had never sought the same access. That official was subsequently placed on administrative leave. A second request, signed personally by Gottumukkala, went forward. His signature acknowledged the counterintelligence polygraph requirement mandated by the originating agency. Career staff arranged the examination.
In late July 2025, he took the polygraph.
He did not pass.
He took it again.
He did not pass again.
According to the March 13, 2026 congressional letter led by Rep. James Walkinshaw (VA-11) and signed by four colleagues — citing information provided to House Homeland Security Committee staff by one of the suspended employees — Gottumukkala failed two counter-intelligence scope polygraphs required for access to the program. The letter was addressed to the inspectors general of DHS and the Intelligence Community.
Two failures. The same program. At an agency whose statutory mission is protecting federal networks from adversaries.
Congress Asked. He Denied It.
At a House Homeland Security Committee hearing on January 21, 2026, ranking member Bennie Thompson (D-MS) asked Gottumukkala directly whether he had failed a counterintelligence polygraph. Gottumukkala told Congress he “did not accept the premise of that question.”
The Walkinshaw letter, filed six weeks later, states that he “falsely accused career CISA staff of providing incorrect information” and asks whether his actions to “obstruct or retaliate against DHS employees for disclosing his two counter-intelligence polygraph failures to the Director of National Intelligence constitute a Prohibited Personnel Practice under 50 U.S. Code § 3234.”
The lawmakers also ask whether CISA’s Chief Security Officer ever alerted ODNI, as federal statute requires following a polygraph failure, and whether ODNI engaged a review of Gottumukkala’s clearance.
The answers remain publicly unknown.
The Staff Who Enforced the Rules Were Punished
On August 1, 2025, acting DHS Chief Security Officer Michael Boyajian sent letters to six CISA employees suspending their classified access. Their stated offense: providing false information to the acting director about the necessity of a polygraph. They had not created the requirement. They had followed the conditions the originating agency laid down. The practical offense was arranging a procedure that produced an embarrassing result for a political appointee.
By December, twelve officials — among them several Trump appointees — had described the episode to Politico on background despite the risk to their own careers.
“Instead of taking ownership and saying, ‘Hey, I screwed up,’ he gets other people blamed and potentially ruins their careers,” one current official said. “We’re a sinking ship.
We’re like the Titanic,” said another.
As of February 2026, those employees’ clearances remained revoked and they remained on administrative leave — more than six months after the original letters.
DHS’s public response came from Assistant Secretary Tricia McLaughlin, who stated that Gottumukkala “did not fail a sanctioned polygraph test” (the emphasis is mine.) The statement does not assert he passed a test. It does not dispute that counterintelligence examinations took place. It does not deny that the SAP (Special Access Program) owner required one as a condition of access, or explain why his own signature on the access request would not have alerted him to that condition. Under DHS’s reading, the polygraph was unauthorized because political leadership had never formally approved the access request in the first place — which would mean Gottumukkala pursued restricted intelligence access after being denied, after the official who denied him had been conveniently removed.
Neither interpretation is flattering.
The ChatGPT Incident
The polygraph failures were not the only security lapse. Between mid-July and early August 2025 — the same period as the first polygraph — Gottumukkala uploaded at least four documents marked “for official use only” to the public version of OpenAI’s ChatGPT. The uploads triggered automated cybersecurity alerts designed to detect theft or unintentional disclosure of government materials from federal networks, generating several alerts in the first week of August alone. He had personally requested special authorization from CISA’s Chief Information Officer to use OpenAI’s ChatGPT shortly after joining the agency, despite the fact that the tool is blocked for most DHS employees over concerns that sensitive information could be retained outside federal systems. Data entered into the public version of ChatGPT can be incorporated into OpenAI’s training data and exposed to hundreds of millions of users.
After the alerts surfaced, Gottumukkala met with CISA’s CIO Robert Costello, its chief counsel, and DHS’s acting general counsel to assess potential harm. CISA spokesperson Marci McCarthy described the usage as “short-term and limited” and said he had operated under an authorized temporary exception. Costello, the CIO who sat across from him in those meetings, subsequently tried to be dismissed by Gottumukkala in January 2026 — an effort blocked by other senior political appointees, but one that accelerated his departure from CISA and federal service.
Chair of the Senate Judiciary Committee Senator Chuck Grassley (R-IA) sent CISA a letter pressing the agency about the ChatGPT incident. As of this writing in early April 2026, CISA has not responded.
In his first weeks on the job, the man running the agency responsible for federal cybersecurity hygiene had uploaded government documents to a commercial AI platform, failed a counterintelligence polygraph, then failed a second one.