The Industry That Fights Governments for a Living Won't Fight This One
On clearances, salaries, and the structural silence of the American infosec community.
I have spent the better part of two decades in information security. I was one of those kids who came up through hacker culture, then managed to professionalize those skills into a career.
And lately, watching the cybersecurity community go quiet while the Trump administration dismantles the country’s defenses, I keep asking myself the same question I’m about to try to answer.
Why aren’t we doing something? We fight nation-state hackers for a living. We have the skills. Many of us hold values that are directly threatened by what’s happening.
Where is everybody?
Answering that honestly requires pulling apart several threads at once: money, clearances, the peculiar political inheritance of hacker culture, the structural position of technical professionals under capitalism, and a community that has quietly confused professional discretion with moral neutrality.
The SentinelOne Test
If you want to understand why the cybersecurity industry is silent, start with what happened to Chris Krebs. Krebs was the founding director of CISA, the government’s civilian cybersecurity agency.
Our community has generally had a positive view of CISA—in no small part due to the years-long visible efforts of their senior leadership, including Krebs, to create lines of integration with information security communities of practice and create a sense of democratic participation in the defense of the nation.
Many sectors which are critical to national defense are under the control of private enterprises, so it is similarly important to build these relationships—as well as relationships with foreign organizations tasked with the defense of their own respective nations—and they had, partly through forging relationships with noted influencers and increasing their visibility at industry events.
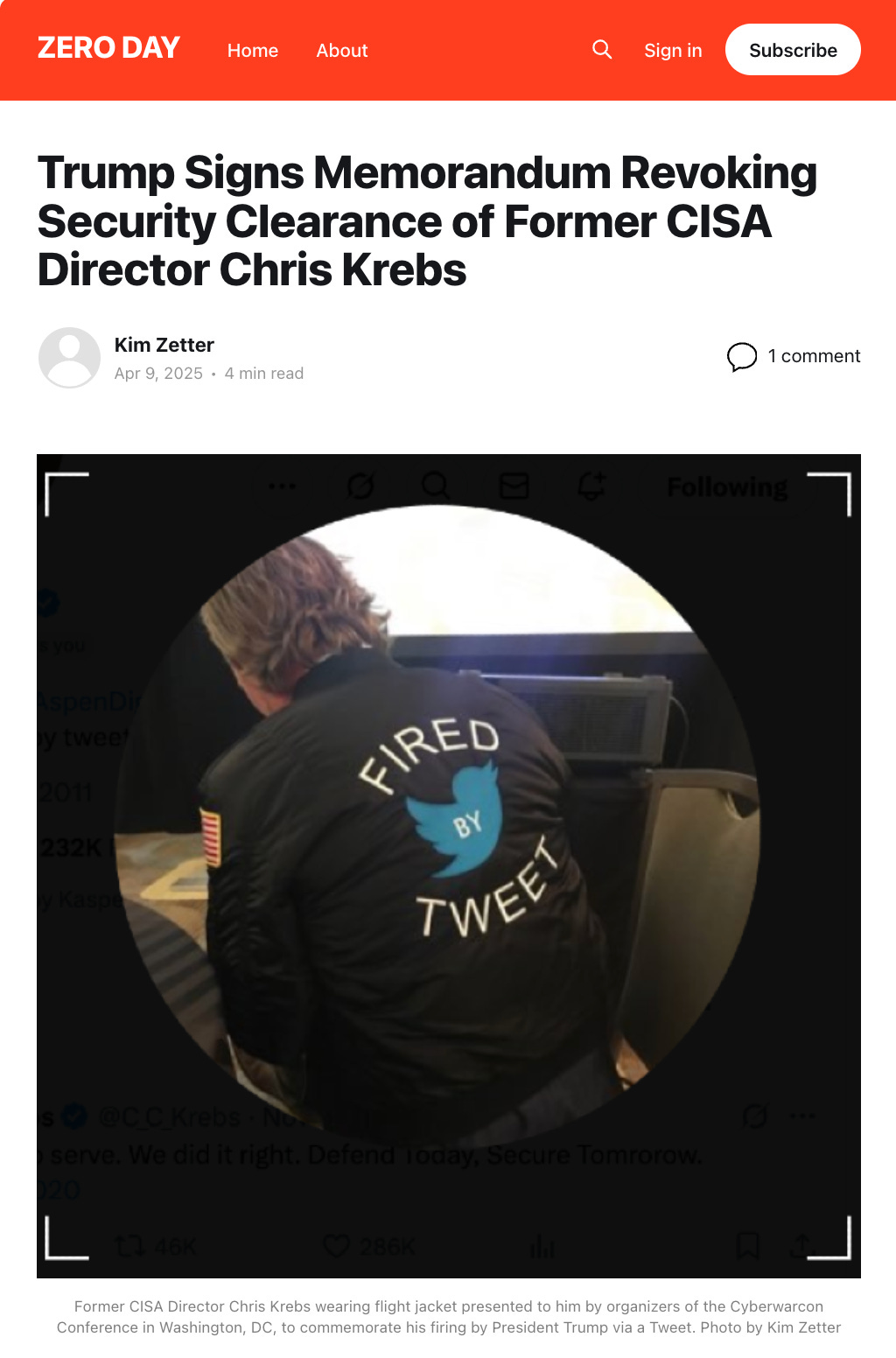
Trump fired Chris Krebs unceremoniously via tweet in November 2020 for working to counter disinformation that the presidential election was not secure. At the 2021 Cyberwarcon conference, organizers presented him with a flight jacket reading “FIRED BY TWEET,” and everybody clapped.
In April 2025, the joke stopped being funny: Trump issued a Presidential Memorandum naming Krebs in its title.
For lawyers and process nerds: that one is technically a Presidential Memorandum rather than an Executive Order, but in practice it functions the same way: it directs the executive branch, carries binding instructions for agencies, and can be enforced unless it conflicts with statute or the Constitution. The differences are mostly procedural: Memoranda don’t have to be printed in the Federal Register, they don’t have to spell out the president’s specific legal authority the way orders do under 1 C.F.R. § 19.1, and the budget office doesn’t need to issue a formal “Budgetary Impact Statement” for them.
The effect of the Memorandum was the revocation of Krebs’ security clearance, the start of a Justice Department investigation into his government service, and the suspension of the clearances of every employee at SentinelOne, where Krebs worked as chief intelligence and public policy officer. No evidence supported the White House memo’s accusation that he had been “suppressing conservative viewpoints,” and no explanation was offered for why SentinelOne’s entire workforce should be punished. Within a week, Krebs resigned, saying the fight was one he needed to take on outside the company.
Reuters contacted 33 of the largest U.S. cybersecurity companies for comment.
Thirty-two either declined or did not respond. A single voice of opposition came from the Cyber Threat Alliance, a nonprofit, whose president Michael Daniel said: “Targeting a company because the president does not like someone in the company is an example of the very weaponization of the federal government the memo claims to be combating.”
Katie Moussouris, founder of Luta Security, was blunt: “I don’t think it’s feasible for cybersecurity companies to have a broader response on this. The risk is just too high.”
An anonymous executive put it more plainly to Reuters: “If they are willing to crush Mr. Krebs, what do you think they’ll do to me?”
The Dismantling
The act against Krebs was not an isolated act of retribution. He was a demonstration project—and the demonstration worked!—because it ran in parallel with a systematic campaign to hollow out America’s cybersecurity infrastructure.
CISA entered fiscal year 2025 with roughly 3,400 employees. By December 2025, that number had fallen to approximately 2,400. Trump’s FY2026 budget proposes cutting the agency’s funding by $495 million, a 17% reduction, eliminating over a thousand authorized positions. Election Security has been entirely zeroed out. Forty-five million dollars stripped from Cyber Defense Education and Training. Seventy million from the National Risk Management Center.
In April 2025, the CVE program nearly collapsed. CVE is the global system for identifying and tracking software vulnerabilities, and it underpins virtually every security operation on Earth. MITRE’s government contract was allowed to approach expiration before CISA threw together a last-minute extension. The system survived. But nobody who watched it happen could avoid the obvious implication: even the most fundamental shared infrastructure of cybersecurity is expendable when it falls within the budget-cutting blast radius.
General Timothy Haugh, who led both the NSA and U.S. Cyber Command, was fired along with his deputy, Wendy Noble. No official rationale was offered. DHS Secretary Kristi Noem took the stage at the RSA Conference and called CISA a “Ministry of Truth,” accusing it of deciding “what was truth and what was not.” She was referring to the agency’s role in debunking election misinformation that Trump still insists was censorship.
By January 2026, the escalation had reached a kind of absurdist peak. CISA, the FBI, and the NSA all pulled out of the RSAC Conference after the event’s organizer hired former CISA director Jen Easterly as CEO. Easterly is a 25-year Army veteran and political independent whose offense was criticizing the administration’s loyalty mandate at the previous year’s conference. West Point had already rescinded a job offer to her after a far-right activist objected. The federal government withdrew from the world’s largest cybersecurity gathering because it didn’t like the new boss—one who was, until quite recently, their own well-respected boss.
All of this while Chinese state-sponsored hackers remain positioned inside American critical infrastructure. As Easterly wrote on LinkedIn before Trump’s allies forced her further from public life: “As experienced leaders exit and key roles remain vacant, our nation’s cyber defenses are at risk of being dangerously degraded.”
The Government as Threat Actor
This is the part that should unsettle everyone in my field.
We train to defend against Advanced Persistent Threats, use acronyms like APT28 and APT41 and Volt Typhoon, write detection rules, build threat models, share indicators of compromise. Our entire conceptual apparatus assumes the threat actor is foreign and that the U.S. government is, broadly speaking, on our side.
Then came DOGE. Elon Musk’s operatives gained access to Treasury payment systems, OPM personnel databases, and IRS records with minimal security vetting. Alan Butler, executive director of the Electronic Privacy Information Center, told Politico that their access to federal data was “an absolute nightmare.”
Bruce Schneier at Harvard said government systems are now less secure because of DOGE’s actions. Axios reported on the insider threat implications of granting rapid access to individuals with unclear backgrounds and undisclosed conflicts of interest. A former DHS Chief Privacy Officer described what happened as “a data breach of exponential proportions.”
In any other context, we would call this an insider threat. We would write an incident report, recommend access revocation, conduct forensic analysis. But the people who did it answer to the president, and the people who would normally investigate are being fired or silenced. Nobody has written a TTP report for DOGE. Nobody has published a MITRE ATT&CK mapping for an executive branch that treats its own government’s data as a personal resource.
Our frameworks were not built for this.
Who We Are, and Why That Matters
You can’t understand how this community responds without understanding where it came from. Information security descends from hacker culture, and hacker culture’s founding ethic was libertarian in the older, pre-partisan sense: distrust of authority, commitment to open information, and an unwavering belief that technology could route around institutional power. Cypherpunks who built the encryption tools we still depend on saw cryptography as a liberating force against government surveillance.
The politics are not neatly left or right. They are anti-authoritarian, which maps onto anarchism for some, market libertarianism for others, progressive activism for still others. Walk around DEF CON and you will find people who think open source is a grand anarchist experiment sitting next to people who think the Second Amendment is a cybersecurity posture. Collective political action can be difficult when the only shared conviction is some vague skepticism of centralized power.
Demographics complicate this further. Women make up 22% of the cybersecurity workforce. LGBTQ people, including a visible contingent of trans women hackers and security researchers, have carved out real cultural space in this industry—from long‑running events like Queercon at DEF CON, which I have personally attended and found to be great fun, to highly public practitioners like Alissa Knight who’ve made it easier for others to imagine themselves here. Plenty of people in this industry have skin in the game when it comes to the policies this administration is pursuing.
Yet the workforce remains overwhelmingly white and male. People with the greatest personal stakes in resisting are also the most vulnerable in the workplace, and the least able to speak out safely. Meanwhile, the white, male, credentialed, senior professionals who hold the most structural power face the least direct personal threat.
Conferences celebrate minority members with panels and mentorship programs, but none of that has translated into collective defense when those same members face real-world policy harm.
Does the Culture Support MAGA?
No. Not broadly. But the picture has nuance that a flat denial would miss.
At RSA 2025, Chris Krebs drew thunderous applause for saying “we should be outraged. Absolutely outraged.” Moussouris told reporters, “Everybody feels the same way I do. Nobody is authorized to say anything officially.” An open letter from the Electronic Frontier Foundation gathered more than 40 prominent signatories condemning the Krebs executive order. A State Department employee at the conference, speaking on condition of anonymity, called Secretary Noem “just a puppet.”
Overwhelmingly, sentiment in this community runs against what the administration is doing. It finds expression in private Slack channels, anonymous quotes to reporters, standing ovations at conferences. What it does not produce is organized, public, sustained resistance.
I should be transparent about where I sit in all of this. I was never fully anonymous in the communities I came up through, and I haven’t stopped using my voice. If anything, I’ve become far more strident since 2020, when I watched the security community fail to mount any serious response to the disinformation campaigns and election targeting that defined that cycle. Some of that targeting was directed at me personally. Those events fully clarified something I might have already known: silence in this industry is a choice, and it benefits whoever is running the operation.
Which brings me to the one moment when a real part of the community did speak up. In late April 2025, the EFF organized an open letter to the White House demanding that the Krebs investigation be dropped and SentinelOne’s clearances reinstated. I signed it.
The initial version carried names like Ron Rivest, Matt Blaze, Bruce Schneier, Jeff Moss, Alex Stamos, and Gabriella Coleman—people whose careers are established and reputations large enough to absorb the hit. Within days, the signature count blew past 400. The version I have in front of me now carries over 730 names.
Look at who signed, and a pattern emerges. About 80% included a professional title or affiliation, which in this context is itself an act of exposure. Roughly a quarter hold senior positions: C-suite executives, CISOs, directors, distinguished engineers, endowed professors at MIT, Princeton, Stanford, Georgetown, Columbia. CSO Online called it “a who’s who of the cybersecurity intelligentsia.”
But the bulk of signatories, close to half, are mid-career practitioners: security engineers, analysts, architects. People with titles like “Cybersecurity Professional” or “Security Analyst at Black Hills Information Security.” These are people who don’t have endowed chairs to fall back on.
One name stands out for a different reason: Jonathan Kamens, who listed his title as “Former (fired by DOGE) Information Security Lead and Advisor to the CTO, U.S. Department of Veterans Affairs.” He signed as an original signatory, not an open one. He had already lost his job, and chose to make that visible.
The letter mattered. But 730 names out of a global cybersecurity workforce of over 5 million is vanishingly small. And as Krebs himself told Politico six months later, the executive order remained in force, his clearance was still revoked, and SentinelOne was still dealing with the fallout. Solidarity was expressed and nothing changed.
A real but minority pro-MAGA tendency does exist within the community, concentrated in military and intelligence-adjacent subcultures and in parts of the crypto and prepper worlds that overlap with hacker culture. Some of this traces back to the libertarian strand of hacker politics that has always been comfortable with right-wing anti-government rhetoric. But saying the culture “inherently supports MAGA” gets it wrong.
What the culture inherently supports is self-preservation. At this time, self-preservation and silence feel indistinguishable.
The Professional Managerial Trap
A body of left-wing theory explains what is happening here. In 1977, Barbara and John Ehrenreich coined the term “professional-managerial class” (PMC) to describe salaried mental workers whose function is “the reproduction of capitalist culture and capitalist class relations.” They don’t own capital. They manage it, protect it, optimize it, and discipline the people who produce it.
Infosec professionals fit that description almost too well. We design access controls, write acceptable-use policies, implement data-loss prevention, monitor employee behavior on corporate networks, and enforce compliance regimes. Our professional purpose, at its structural core, is to keep the systems through which capital flows running without disruption. The trains must run on time. When the Ehrenreichs described the PMC’s relationship to the working class as “objectively antagonistic,” they could have been describing the person who configures your company’s endpoint detection and decides what you’re allowed to plug into your laptop.
A recent analysis in Jacobin puts a fine point on it: the PMC are “servants of capital, but also have a disdain for capitalism.” I recognize that tension in myself and in most of my peers. Many of us believe, sincerely, that we are protecting people: hospitals from ransomware, election infrastructure from foreign interference, critical infrastructure from catastrophic failure… Structurally, most of us work for corporations or government agencies whose primary interest is protecting capital, intellectual property, and state power. The sincerity is real but the paycheck comes from somewhere else.
And the paycheck is definitely generous. The average U.S. cybersecurity salary: $147,000. Directors and middle managers average $175,000. CISOs regularly clear $200-400K, and top earners exceed $1 million annually. That kind of money buys houses, private school tuitions, stacked retirement accounts, and a way of life that becomes very difficult to risk for the sake of a LinkedIn post.
Security clearances make the trap even tighter. A large portion of the infosec workforce holds or aspires to government clearances which can sometimes unlock lucrative contracts and often the most interesting work. As the Krebs case demonstrated, those clearances are revocable by presidential fiat. When your clearance is your career, and the president has shown he will use clearance revocation as punishment, speaking out goes beyond professional risk.
The Retreat from the Narrative Battlefield
One of the most consequential decisions the infosec community has made in recent years is leaving X/Twitter.
I understand the impulse. Musk’s platform became hostile to the values many in this community hold. Harassment spiked. Trans users were targeted relentlessly. Moderation collapsed. Leaving felt like self-preservation—in many cases, it was.
But Mastodon and Bluesky are not what Twitter was. They are smaller, more fragmented, built for conversation among the like-minded, where security pros talk to other pros about security. Pleasant, sometimes useful, but rarely political engagement in any meaningful sense. Leaving X was a moral exit, not a strategic one. It ceded the largest public forum where technical expertise could have shaped political discourse to bad actors who have been more than happy to fill the vacuum with nonsense.
The progressivist web chose comfort over influence. A community that prides itself on understanding adversarial thinking failed to think adversarially about information warfare.
The Professional Culture of Discretion
One more factor deserves attention because it’s one that is highly specific to this field.
Information security professionals are generally discreet. Operational security is not just a practice, but an identity marker. We often don’t disclose vulnerabilities before they are patched, share intelligence outside trusted channels, or draw attention to ourselves. These habits serve real purposes in their proper context, but they have metastasized into a professional culture where any public political statement feels like a violation of norms.
“We protect systems, not take sides” has become the industry’s equivalent of “just following orders,” which provides cover for inaction that handily serves the interests of whoever currently controls the systems we protect or can successfully apply pressure to its owners.
When Politico described a “typically nonpartisan community beginning to vocalize its dissent” at RSA, it was describing something real. But “beginning to vocalize” in the spring of 2025, months into the dismantling of the American experiment, was already far too late. And vocalization in the form of anonymous quotes and conference applause will never be the same as action.
What Would Action Look Like?
I don’t have a clean answer, but I know how it doesn’t look: migrating to Mastodon to post for an audience that already agrees with you, signing an open letter and going back to work on your government contract, or applauding Chris Krebs at a conference and then telling Reuters “no comment” when asked about SentinelOne.
The cybersecurity community has an asymmetric capability that almost no other professional class possesses. We are people who understand, at a technical level, how the systems of power actually work, who know where the data lives, how it moves, and what is exposed.
The anti-capitalist analysis would say this power will never be wielded against the system because the people who hold it are too deeply embedded in the system’s rewards. The PMC critique holds that professionals whose livelihood and identity depend on capitalist institutions will, in the final analysis, choose those institutions over solidarity with the people those institutions harm.
So far, the evidence supports that reading.
But the Ehrenreichs themselves acknowledged that as working conditions and pay of the PMC deteriorate, alignment with the broader working class becomes possible, even if never guaranteed and always fraught.
Clearances are being revoked. Budgets are being slashed. The CVE program nearly died. Agencies are being gutted. The government pulled out of the industry’s own conference over a hiring decision. Conditions that once made silence feel like prudence are rapidly becoming conditions where silence feels like complicity.
I cannot tell you whether this community will recognize that shift in time. But the window in which inaction can be mistaken for neutrality is closing fast.


Appreciate the deep dive into the mindset of those in the cyber security profession. Especially in regards to their many differing motivations for silent complicity. As someone on the outside so to speak, I've had a very difficult time understanding how so many of the institutions, ones whose purported missions are protecting national security and the people of our country, seem to have failed quite spectacularly in a number of critically important areas. Your article helped provide some of those answers.
Ultimately it seems, our nation's overall pampered quality of life and comfort with the status quo is proving to be one of our biggest vulnerabilities. As your article points out, the cyber security realm is no exception. What's frustrating is that at this moment in time, one of our strongest weapons to fight back against the billionaire class, collectively speaking, is organized strikes and boycotts. Hitting them where it impacts them the most, in their bank accounts and stock portfolios, would require almost no violence, death, or physical destruction. Once they realized that we've finally awoken to the fact that WE hold all the power, it wouldn't be long before they caved.
Unfortunately though, effectively launching that attack requires that we all accept some short term hardships and suffering for the long term better good. This is a trade off that our nation's population, at least thus far, continues proving that it's unwilling to take. The irony, of course, is that by refusing to accept that short term suffering and do what's necessary, we're in turn dooming ourselves to far greater pain and suffering, and for what will likely be a far longer period of time...